The Atomic Mandate: Engineering Certainty in the Quantum Era.
Building the most powerful machines in history requires an equally disciplined approach to security. We are establishing the technical roadmap for post-quantum cryptography and calling on the global community to match our precision in securing the digital frontier.
Checking read-aloud support…
The Atomic Mandate
In my laboratory, we work at the absolute limit of what is physically possible. We place individual phosphorus atoms into a silicon lattice with 0.13-nanometer precision. When you work at that scale, you learn very quickly that nature doesn’t give you anything for free. Every error, every bit of noise, and every oversight is magnified.
We are currently in a global race to build a functional, error-corrected quantum computer. My team at Silicon Quantum Computing (SQC) isn’t just theorizing; we are delivering multi-qubit, multi-register processors with 99.99% fidelity. But as we succeed in the lab, we are creating a fundamental paradox for the world outside: the very machine that will unlock the secrets of photosynthesis and room-temperature superconductivity will also render our current digital security architecture irrelevant.
If you think this is a future problem, you are failing to account for the physical reality of the data we are protecting today.
The Physics Of The Threat
Most people view the quantum threat as a quantitative shift, a computer that is simply faster. That is a dangerous simplification. A cryptographically relevant quantum computer represents a qualitative shift in how information is processed.
By leveraging entanglement and superposition, these machines can perform Shor’s algorithm to factor large integers, the very foundation of RSA and ECC encryption, at speeds that make the age of the universe look like a lunch break.
We are also already seeing the logic of harvest now, decrypt later attacks. Malicious actors are intercepting high-value, long-term data today, including sovereign secrets, intellectual property and critical infrastructure schematics, knowing that the key to unlocking it is currently being engineered in labs like mine. If your data needs to remain secret for the next 20 years, it is already at risk.
The Architecture Of Resilience
We cannot afford to go into this half-cocked. Transitioning a global economy to post-quantum cryptography is perhaps the most significant engineering migration in human history. It requires a level of discipline that matches the precision we use to build the qubits themselves.
1. The Engineering Of Crypto-Agility
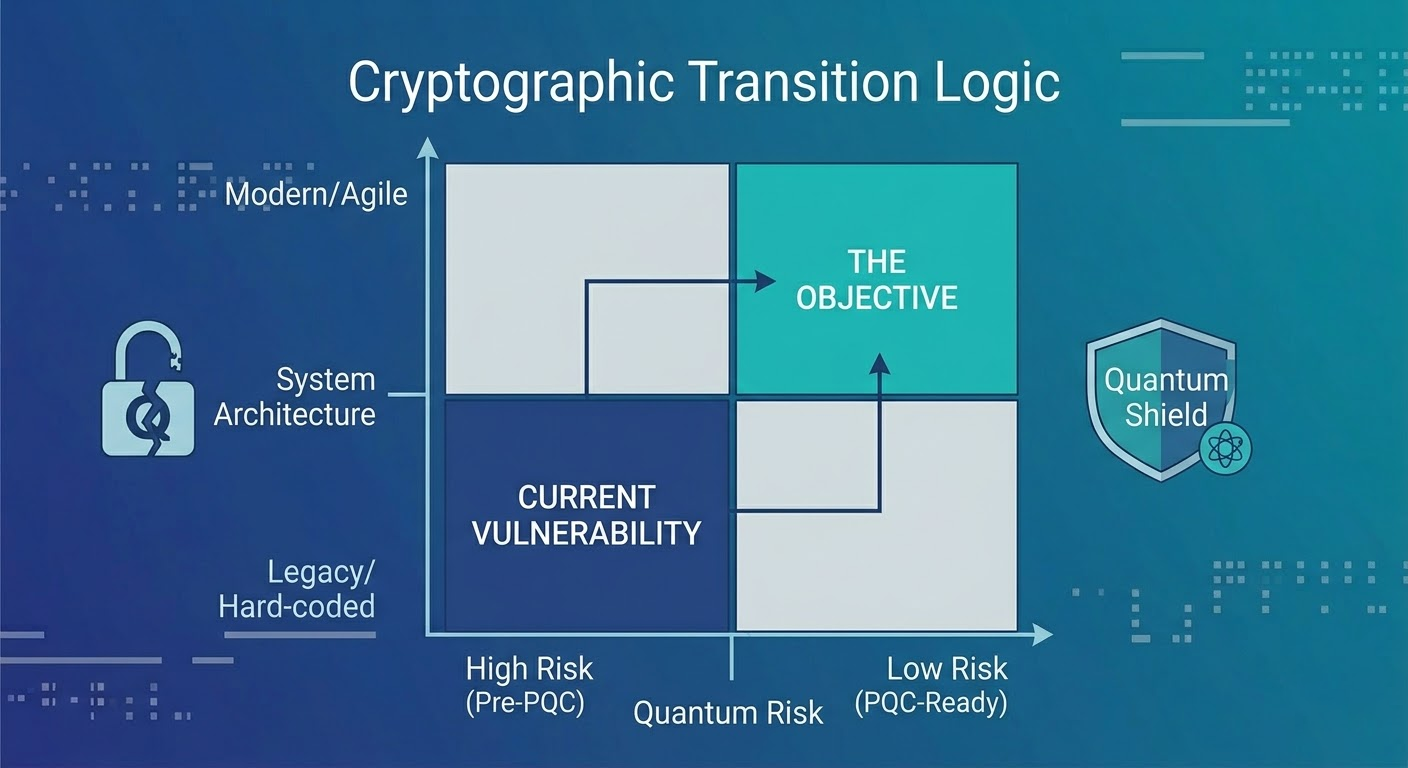
In the past, cryptography was hard-coded and static. In a quantum-active world, that is a fatal flaw. We must move toward crypto-agility: the structural ability to swap out cryptographic primitives without rebuilding the entire stack.
You need to inventory the stack first. Organizations must identify every instance of RSA and ECC within their environment. You cannot protect what you cannot see.
You then need modular implementation. Security has to be decoupled from the application layer so that when NIST finalizes a new standard, such as ML-KEM or ML-DSA, it can be deployed across the fleet via a single update rather than a decade-long hardware refresh.

2. Anchoring Security In Material Reality
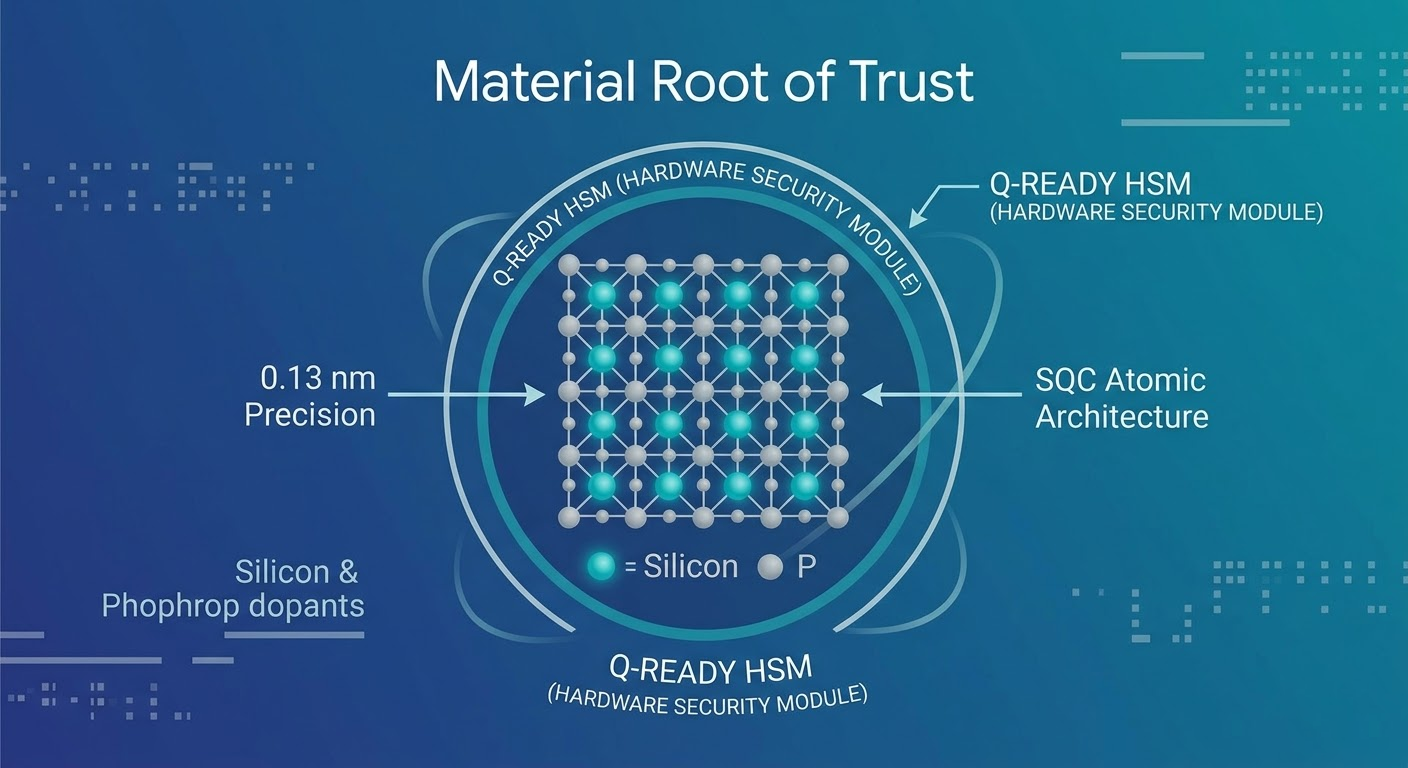
At SQC, we focus on silicon because it is the most well-understood material on Earth. We leverage billions of dollars of existing semiconductor R&D to ensure our qubits are stable.
Digital security must take the same approach. We should be prioritizing Hardware Security Modules that are PQC-compliant at the silicon level. By baking quantum resistance into the physical hardware, including the security chips in our phones and the servers in our data centers, we create a root of trust that is not dependent on fragile software patches.
3. Eradicating Global Fragmentation
The quantum world is universal, and our defense must be as well. If different regions adopt disparate, non-interoperable standards, we create seams in the global data fabric. These seams are where the most sophisticated attacks will occur.
We must align globally with the NIST-selected algorithms to ensure that the quantum shield is continuous and without gaps.
4. The Cloud As A Strategic Necessity
Migrating legacy on-premise systems to PQC is an almost impossible task for most enterprises. The most viable path forward is a rapid transition to quantum-ready cloud infrastructure. Major providers are already integrating quantum-resistant filters into their key exchange protocols.
By moving to the cloud, organizations effectively outsource the most difficult engineering parts of the quantum transition to teams that have the scale to handle it.
The Reality Check
I am an optimist. You have to be to spend twenty years trying to control a single atom. But my optimism is grounded in hard work and deep thinking. We are building the most powerful tool in human history, but we are building it in a world that is currently locked behind doors we are about to provide the keys for.
We have the roadmap. We have the NIST standards. We have the engineering talent. What we need now is the collective will to treat this transition with the same uncompromising precision we bring to the lab every single day.
The race is on. Don’t be the one caught standing still when the first error-corrected machine comes online.