What to do first if your phone is stolen while unlocked
An unlocked stolen phone can expose messages, email, passwords and recovery routes very quickly. Here, I break down the first actions that help you contain the damage before the situation spreads across more accounts.

Checking read-aloud support…
Why This Topic Matters
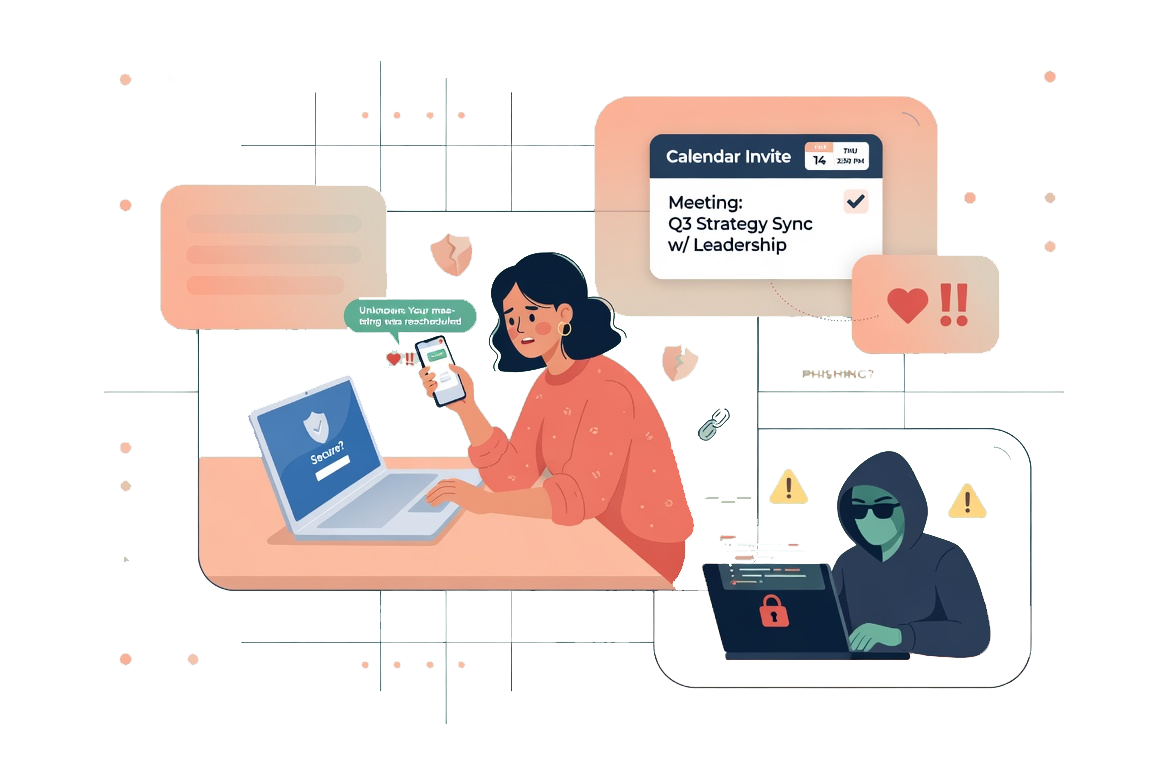
Phone theft is not only about losing hardware. If the device was open, or easy to reopen, it may also expose your main email, saved passwords, payment apps and identity-provider accounts.
That matters because the first few steps after the theft influence how many second-order problems follow. A calm response order can stop the incident from becoming a wider account takeover.
What To Check First
When I want this kind of review to stay practical, I begin with the accounts that can unlock the rest.
That means checking:
- whether you can still reach the device through Find My iPhone or Find My Device
- whether your main email account is still secure
- whether messaging previews, banking apps or saved cards were exposed
- whether the thief could use the phone number for further recovery attempts
The point is not to solve everything at once. It is to secure the accounts that let everything else cascade.
Build A Fast Response Order
The response I prefer is structured rather than improvised.
The routine I would use is:
- mark the phone as lost or lock it remotely from another trusted device
- change the password on your main email and primary Apple or Google account
- review active sessions, banking access and saved payment methods
- contact the carrier if you suspect the number itself could be reused
This order helps because identity and recovery access usually matter more than the handset itself in the first stage.
What Usually Goes Wrong
The common mistake is spending too long trying to physically recover the phone before starting account containment. That instinct is understandable, but it can waste the window in which remote controls and password changes do the most good.
This is why I like response plans that reduce thinking under stress. Good order beats perfect memory.
A Better Baseline
If the phone is stolen while open, speed matters, but so does sequence. Lock the device, secure the main accounts and then widen the review from there.
That is the standard I care about: not a dramatic checklist, but a response that protects the parts of your digital life the phone was connected to.